How To Set Password Complexity In Redhat Linux 7
Fifty-fifty though Linux is secure by design, there are many chances for the security breach. Ane of them is weak passwords. As a Arrangement ambassador, you must provide a stiff countersign for the users. Considering, mostly arrangement breaches are happening due to weak passwords. This tutorial describes how to set password policies such equally password length, countersign complication, password expiration period etc., in DEB based systems like Debian, Ubuntu, Linux Mint, and RPM based systems like RHEL and CentOS.
Set Password Policies In Linux
By default, all Linux operating systems requires password length of minimum six characters for the users. I strongly advice you lot not to go below this limit. Also, don't use your real name, parents/spouse/kids name, or your date of nascence as a password. Even a novice hacker can easily break such kind of passwords in minutes. The good password must e'er contains more than half-dozen characters including a number, a capital alphabetic character, and a special character.
Set password length in DEB based systems
Usually, the password and authentication-related configuration files volition be stored in/etc/pam.d/ location in DEB based operating systems.
To set minimum password length, edit/etc/pam.d/common-password file;
$ sudo nano /etc/pam.d/common-password
Find the following line:
password [success=ii default=ignore] pam_unix.so obscure sha512
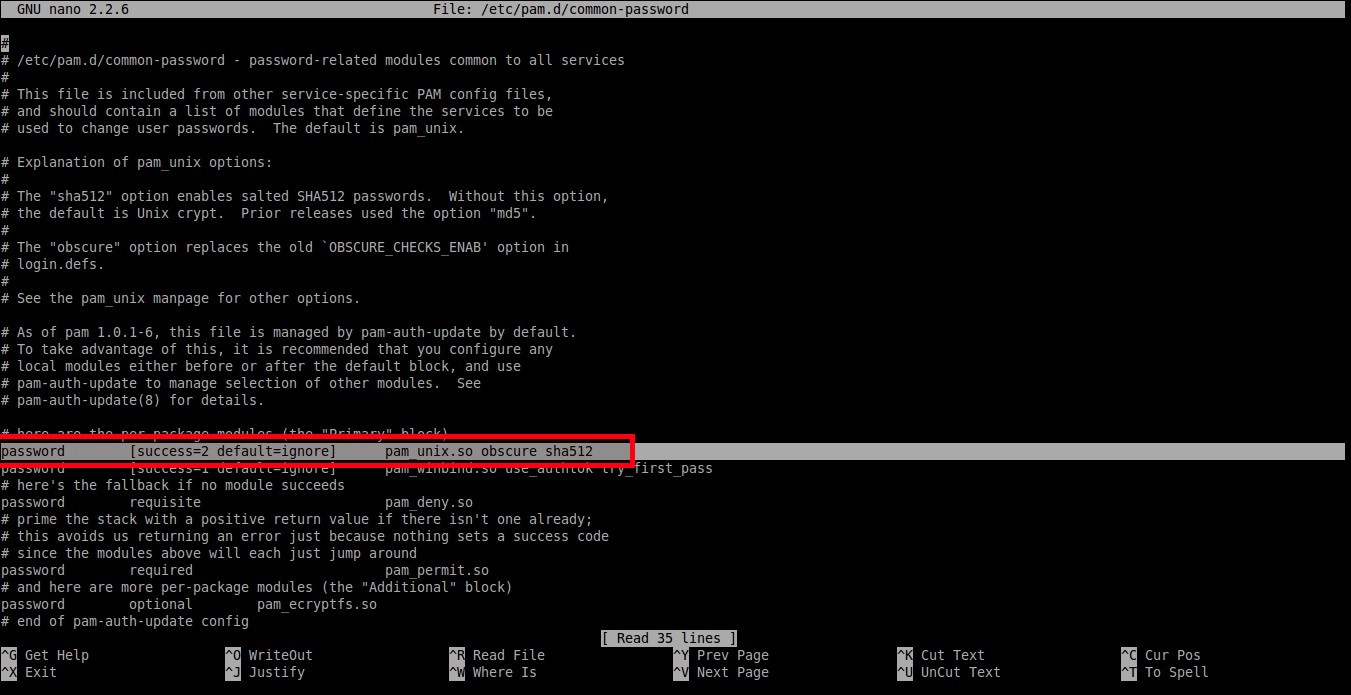
And add an actress word:minlen=8 at the cease. Here I set up the minimum password length as viii.
password [success=2 default=ignore] pam_unix.so obscure sha512 minlen=eight
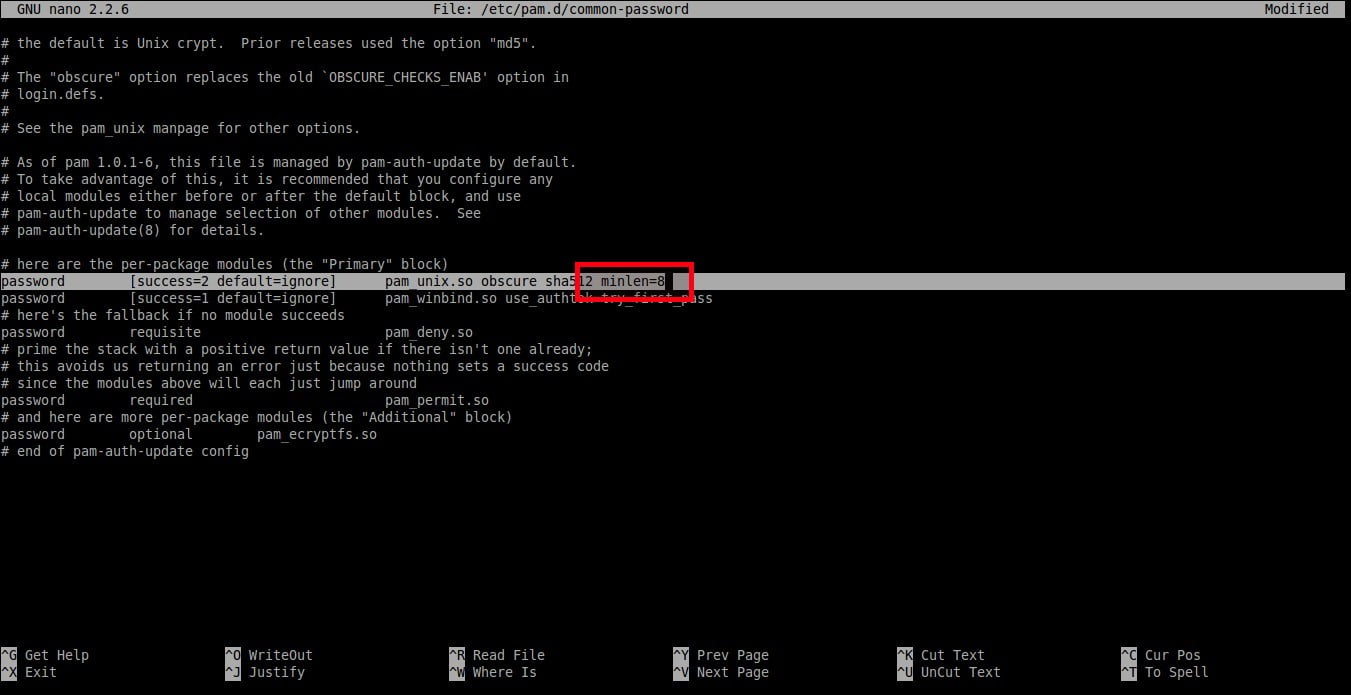
Set password length on DEB-based systems
Salvage and close the file. Now the users can't employ less than 8 characters for their password.
Gear up password length in RPM based systems
In RHEL, CentOS 7.ten systems, run the post-obit control as root user to set password length.
# authconfig --passminlen=8 --update
To view the minimum password length, run:
# grep "^minlen" /etc/security/pwquality.conf
Sample output:
minlen = eight
In RHEL, CentOS 6.x systems, edit/etc/pam.d/organization-auth file:
# nano /etc/pam.d/system-auth
Discover the following line and add the post-obit at the end of the line:
password requisite pam_cracklib.so try_first_pass retry=3 blazon= minlen=8

Set up password length on RPM-based systems.
As per the above setting, the minimum password length is 8 characters.
Ready password complexity in DEB based systems
This setting enforces how many classes, i.e upper-case, lower-case, and other characters, should be in a password.
First install countersign quality checking library using command:
$ sudo apt-go install libpam-pwquality
So, edit/etc/pam.d/mutual-password file:
$ sudo nano /etc/pam.d/common-password
To set at least oneupper-case messages in the password, add a discussion 'ucredit=-1' at the stop of the following line.
password requisite pam_pwquality.so retry=three ucredit=-i

Set countersign complication in DEB based systems
Gear up at least one lower-example letters in the password as shown below.
password requisite pam_pwquality.so retry=3 dcredit=-1
Ready at leastother messages in the countersign equally shown beneath.
password requisite pam_pwquality.so retry=3 ocredit=-1
As y'all meet in the above examples, we have set at least (minimum) one upper-case, lower-case, and a special character in the countersign. You can prepare any number of maximum allowed upper-case, lower-instance, and other messages in your password.
You tin also set the minimum/maximum number of immune classes in the countersign.
The following example shows the minimum number of required classes of characters for the new countersign:
countersign requisite pam_pwquality.and so retry=3 minclass=2
Fix password complexity in RPM based systems
In RHEL 7.x / CentOS 7.x :
To set at least one lower-case letter in the password, run:
# authconfig --enablereqlower --update
To view the settings, run:
# grep "^lcredit" /etc/security/pwquality.conf
Sample output:
lcredit = -1
Similarly, set at least one majuscule in the password using control:
# authconfig --enablerequpper --update
To view the settings:
# grep "^ucredit" /etc/security/pwquality.conf
Sample output:
ucredit = -ane
To prepare at least one digit in the password, run:
# authconfig --enablereqdigit --update
To view the setting, run:
# grep "^dcredit" /etc/security/pwquality.conf
Sample output:
dcredit = -1
To set at to the lowest degree 1 other character in the password, run:
# authconfig --enablereqother --update
To view the setting, run:
# grep "^ocredit" /etc/security/pwquality.conf
Sample output:
ocredit = -1
In RHEL 6.x / CentOS six.x systems, edit/etc/pam.d/system-auth file every bit root user:
# nano /etc/pam.d/organisation-auth
Find the following line and add together the following at the end of the line:
countersign requisite pam_cracklib.so try_first_pass retry=3 type= minlen=8 dcredit=-ane ucredit=-1 lcredit=-one ocredit=-i
As per the above setting, the countersign must have at to the lowest degree 8 characters. In addition, the password should also take at least one upper-case letter, one lower-instance alphabetic character, i digit, and one other characters.
Set password expiration period in DEB based systems
We are going to set the following policies.
- Maximum number of days a password may exist used.
- Minimum number of days allowed between password changes.
- Number of days alarm given before a password expires.
To set this policy, edit:
$ sudo nano /etc/login.defs
Set the values as per your requirement.
PASS_MAX_DAYS 100 PASS_MIN_DAYS 0 PASS_WARN_AGE 7

Fix password expiration period in DEB based systems
Every bit you see in the to a higher place instance, the user should change the countersign once in every 100 days and the warning message will appear7 days before countersign expiration.
Be mindful that these settings will impact the newly created users.
To set maximum number of days betwixt password change to existing users, you must run the following command:
$ sudo chage -M <days> <username>
To set minimum number of days betwixt password alter, run:
$ sudo chage -m <days> <username>
To fix alert before countersign expires, run:
$ sudo chage -Due west <days> <username>
To display the countersign for the existing users, run:
$ sudo chage -l sk
Here, sk is my username.
Sample output:
Last password change : Feb 24, 2022 Countersign expires : never Password inactive : never Account expires : never Minimum number of days betwixt password alter : 0 Maximum number of days between countersign change : 99999 Number of days of warning before password expires : 7
As you see in the above output, the password never expires.
To alter the countersign expiration menstruum of an existing user,
$ sudo chage -East 24/06/2018 -grand 5 -M xc -I x -W 10 sk
The higher up command volition set password of the user 'sk' to expire on 24/06/2018. Also the the minimum number days betwixt countersign change is prepare 5 days and the maximum number of days betwixt countersign changes is set up to 90 days. The user account will be locked automatically after 10 days and It will display a warning message for ten days before countersign expiration.
Set password expiration period in RPM based systems
This is same as DEB based systems.
Forbid previously used passwords in DEB based systems
You tin can limit the users to set a countersign which is already used in the past. To put this in layman terms, the users can't use the aforementioned countersign over again.
To practice so, edit/etc/pam.d/common-password file:
$ sudo nano /etc/pam.d/common-password
Find the post-obit line and add together the give-and-take'recall=five' at the end:
password [success=2 default=ignore] pam_unix.so obscure use_authtok try_first_pass sha512 recollect=five The to a higher place policy will prevent the users to employ the last 5 used passwords.
Forbid previously used passwords in RPM based systems
This is same for both RHEL 6.x and RHEL vii.x and information technology'southward clone systems similar CentOS, Scientific Linux.
Edit/etc/pam.d/arrangement-auth file as root user,
# vi /etc/pam.d/system-auth
Find the post-obit line, and add remember=five at the end.
password sufficient pam_unix.and so sha512 shadow nullok try_first_pass use_authtokcall back=5
Suggested read:
- iv Like shooting fish in a barrel Ways To Generate A Strong Password In Linux
- How To Check The Countersign Complexity In Linux
- How To Force Users To Utilise Strong Passwords In Debian, Ubuntu
- Titan – A Control line Password Manager For Linux
- Buttercup – A Free, Secure And Cantankerous-platform Password Manager
- KeeWeb – An Open Source, Cantankerous Platform Password Manager
You lot know now what is countersign policies in Linux, and how to set different countersign policies in DEB and RPM based systems.
Source: https://ostechnix.com/how-to-set-password-policies-in-linux/

0 Response to "How To Set Password Complexity In Redhat Linux 7"
Post a Comment